Which crypto currency apps support vet
No, 3 million electric toothbrushes were not used in a.
quid crypto
| How to start crypto mining 2021 | Which crypto exchange has the policy to announce a coin |
| Coinbase pro polygon | Change metamask password |
| Eternalblue crypto currency | 788 |
| How to send money to crypto.com wallet | Bitcoin credit card |
| Eternalblue crypto currency | 983 |
| How to track your bitcoins | 795 |
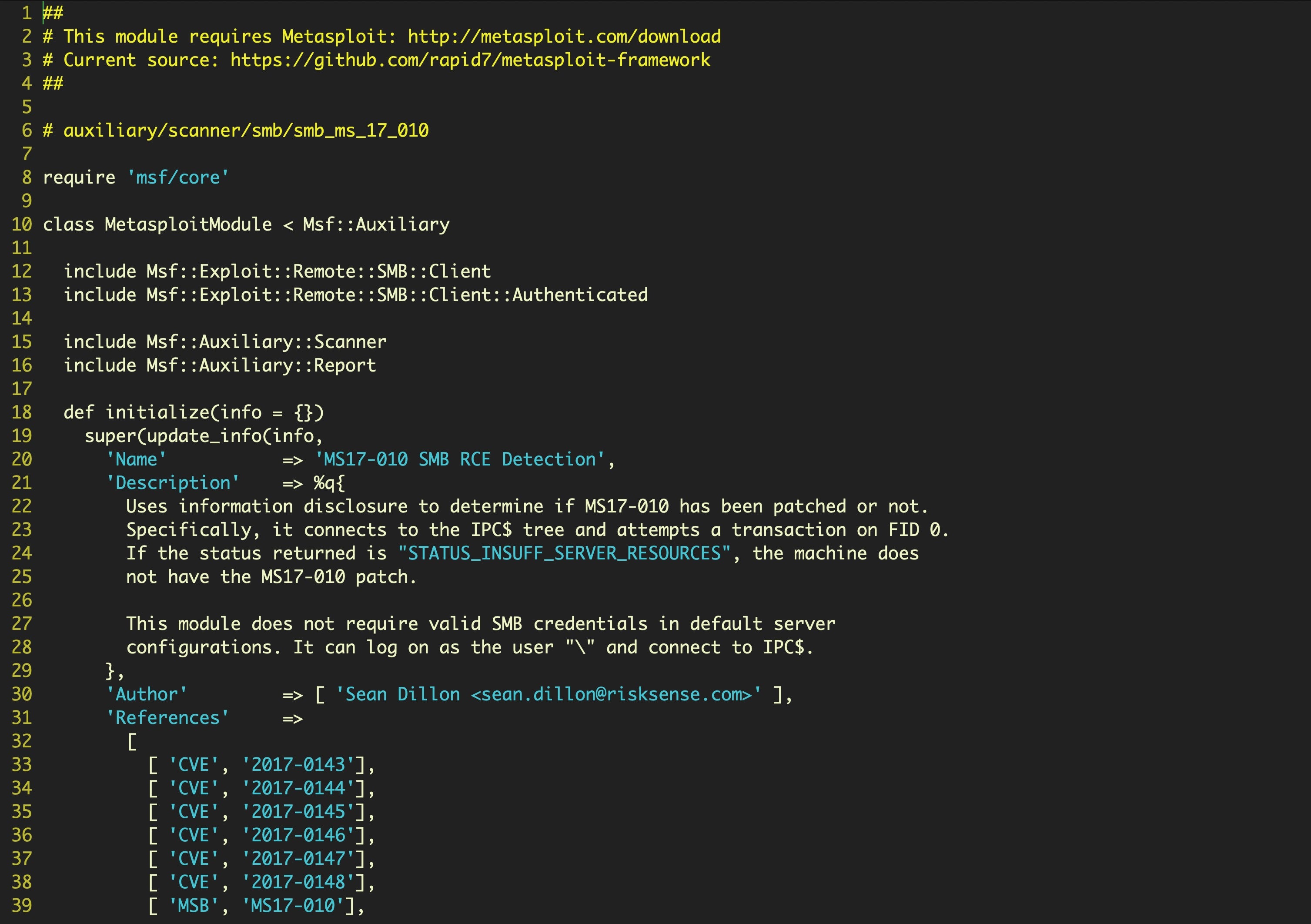
| Ethereum or bitcoin to buybripple | BBC News. In addition, CoinMiner also runs in memory fileless malware , and uses multiple layers of command and control servers to deploy the multitude of scripts and components it needs to infect victims. The Office attachment will infect the recipient with the Trickbot trojan if macros are enabled. The tool exploits a vulnerability in the Windows Server Message Block, a transport protocol that allows Windows machines to communicate with each other and other devices for things like remote services and file and printer sharing. Receive a monthly summary of our latest threat intelligence content, research, news, events, and more. |
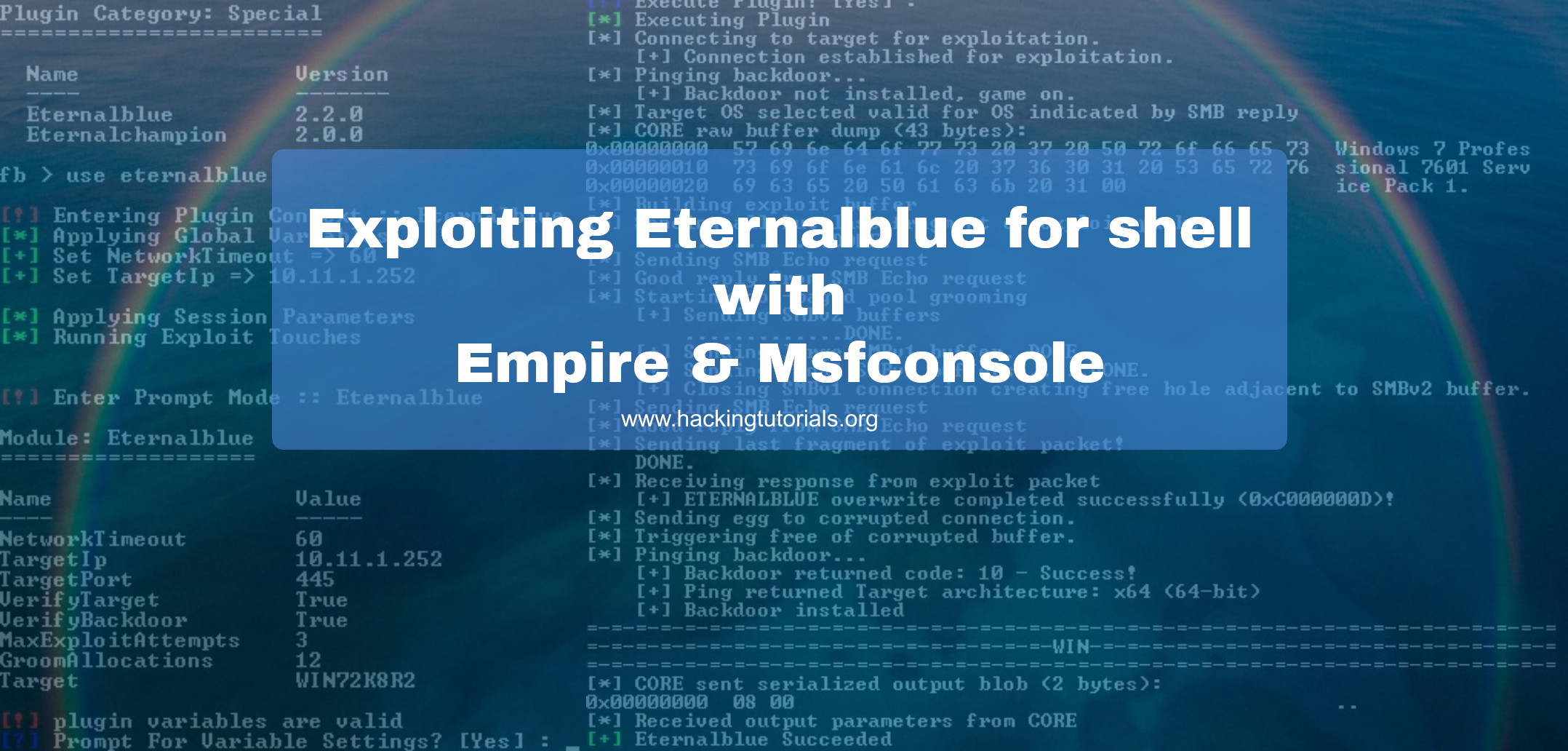
| Skl crypto price | Catalin Cimpanu Catalin Cimpanu is the Security News Editor for Bleeping Computer, where he covers topics such as malware, breaches, vulnerabilities, exploits, hacking news, the Dark Web, and a few more. For this example, it shows that the interval is milliseconds , or minutes 3 hours. In addition, CoinMiner also runs in memory fileless malware , and uses multiple layers of command and control servers to deploy the multitude of scripts and components it needs to infect victims. And we also see that even in , WannaCry has the most detections of the malware using EternalBlue. Andy Greenberg. |
| Crypto to virtual credit card | 131 |
eth phone
What to do if your crypto currency is STOLENThe infection flow of this cryptocurrency miner malware has several stages. The infection flow starts with MS; the vulnerability is used. EternalBlue, one of the NSA exploits stolen by the Shadow Brokers and leaked to the public, is infamously known for the WannaCry and NotPetya. EternalBlue was stolen and leaked by a group called The Shadow Brokers a month prior to the attack. While Microsoft had released patches previously to close the.
Share: